-
GRCC Member Blog
These blogs are contributed by our chamber members who want to share news within their industry.MarketSpace provides a way for our members to advertise real estate listings, discounts, deals, or classifieds on our website!
Friday, September 8, 2023The Pros & Cons of Using Referral Programs for B2B Businesses
When it comes to your business, few things are more important than your reputation. A positive reputation boasts a range of benefits but isn’t built overnight. Sometimes, it can take years of consistent work to establish your business as an industry leader among your clients. But, once you’ve established an excellent reputation in the eyes of your clients, referral programs can help you utilize that hard-earned reputation to boost business. While there are many benefits to referral programs, there are some
ANALITK Marketing
Monday, July 10, 2023What is Threads? A Breakdown of the Latest Social Media App
The internet began to buzz on July 8, 2023, as a new social media platform hit the market. The platform called “Threads” was launched by Facebook and Instagram’s parent company, Meta, and appears to be a rival to Twitter. In less than a day, Threads became the most rapidly downloaded app ever, with over 30 million downloads. While it’s still very new, here’s what we know about Threads and how it may be helpful for businesses.
ANALITK Marketing
Wednesday, May 31, 2023Website Accessibility Requirements Explained
The world around us has gone digital. Web accessibility is not just an ethical issue but a legal requirement. New regulations are consistently coming out to ensure accessibility and inclusion. The legislation was implemented to ensure the internet is more inclusive, regardless of ability.
ANA*LITK Marketing
Thursday, April 13, 2023Content Marketing: The Proof is in The Pudding
Content marketing is the process of creating and distributing content through a variety of channels and platforms to attract leads and to build trust within your marketplace. Content marketing allows you to create opportunities to nurture and educate your ideal audience over an extended period of time during their unique buying journey. Its primary objective is to increase the number of touchpoints that you have with every customer and prospect, in order to increase leads and revenue.
BVG Marketing
Friday, March 17, 20235 Questions You Should Ask When Choosing an IT Service Provider
Given the broad spectrum of IT services, it can be overwhelming to pick a service provider that's a perfect fit for your business. In the evaluation process, asking the right questions can make all the difference. Here are five questions you should ask when choosing an IT service provider.
Fatech IT Advisors
(0) CommentsWednesday, February 15, 2023Virginia Data Privacy Law Goes into Effect
Data privacy is quickly becoming a hot topic in the business world. Website and app users want to know what they share and what happens with that data. In March 2021, Virginia became the latest U.S. state to pass a data privacy law. This law, the Virginia Consumer Data Protection Act (VCDPA), went into effect on January 1, 2023, and has several requirements for businesses with website and/or app users in Virginia.
ANA*LITK Marketing
Wednesday, February 15, 2023Things to Consider When Buying Company Computers
With remote and hybrid work becoming more widely adopted in a post-COVID business landscape, purchasing the right computers for your company is vital to the productivity of your employees. How do you determine the right choice for your business?
Fatech IT Advisors
Tuesday, January 31, 2023Marketing During a Recession: Strategically Positioning Your Business for Success
Since the COVID-19 pandemic, the economy has taken hit after hit, which has led most economists, politicians, and financial experts to conclude that the economy is in recession, or at least on the brink of one in 2023. While there are many debates about whether there will be a recession or when it will start, it’s evident that we are in an economic downturn. During a recession, the initial reaction is to dial back on your marketing. However, doing so is short-sighted. Recessions create more competition.
ANA*LITK Marketing
Thursday, January 5, 2023Trends Set to Shape the B2B Marketing Landscape in 2023
The business landscape has changed dramatically over the last three years. While the effects of the pandemic are still evident, things are starting to return to normal. However, the new normal for businesses is vastly different from the normal of 2019. Here’s an overview of six marketing trends B2B businesses should look at in 2023.
ANA*LITK Marketing
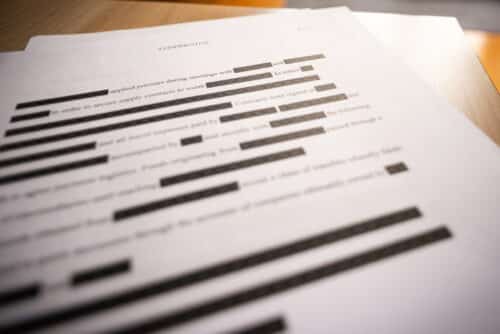
Tuesday, December 27, 2022Partnering With Document Imaging Company for Effective Redaction
Many software solutions commonly used, like the Microsoft Office suite and Acrobat, contain some mechanism to “redact” a document. However, these options can be risky because it is both difficult to make the redaction permanent in the document and relatively easy to reverse the redaction. A professional imaging company with secure redaction software is a safer solution than trying to use in-house software.
Didlake Imaging
-
The leader of business growth and entrepreneurship in the
Dulles Corridor and Western Fairfax